)
Pervasive Security:
a new way of thinking
The Pervasive Security paradigm, created by Reply experts, is a new approach to cybersecurity that integrates seamlessly with modern strategies for digital services implementation.
#Cybersecurity
#Agile
#DevSecOps
#DigitalTransformation
The context
Understanding digital transformation and related trends is fundamental for distinguishing the need for a new approach to cybersecurity.
On a broad scale, digital transformation can take place by either renewing the core or creating new products. In the former, innovative technologies take current practices and make them faster, cheaper, and more effective. In the latter, an organization tries to step outside the core and create something that doesn’t already exist.
Inspired by this duality, we realized that two tailored paradigms were needed for security as well: from that conclusion, Core Security and Pervasive Security were born.
Approach: Renew
Projects related to core system maintenance, stability or efficiency.
Requires traditional, slow moving evolution cycles.
There is little need for business involvement.
CORE SECURITY
.
Approach: Create
Projects that help innovate or differentiate the business
Requires a high degree of business involvement, fast turnaround, and frequent updates. Requires an IT "fast lane" to transform business ideas into applications.
PERVASIVE SECURITY
About Pervasive
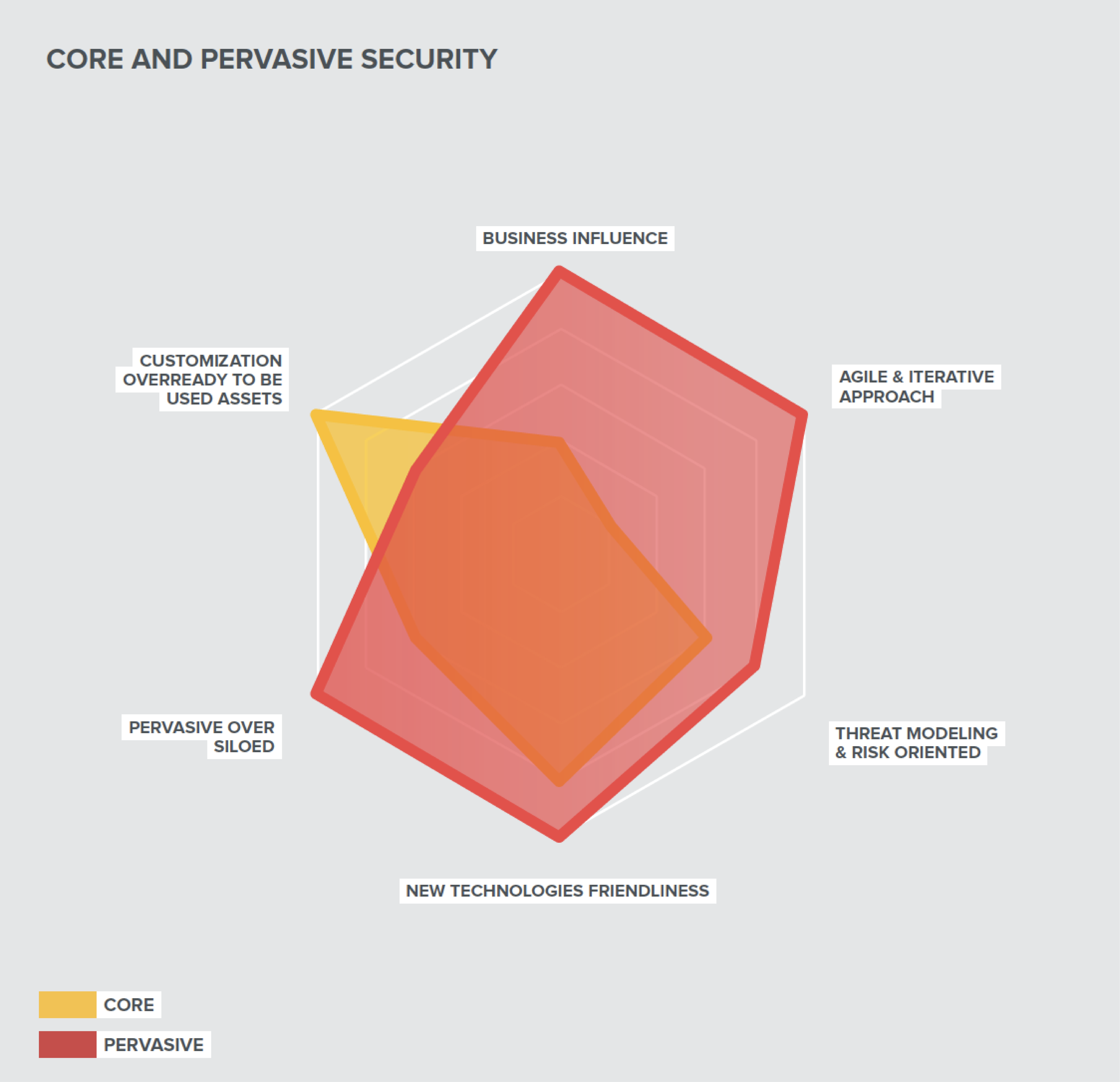
Based on legacy security methodologies, Core Security is fine for initiatives that aim to renew the core. At the same time, to avoid becoming a barrier to innovative digital initiatives and instead become an enabler, cybersecurity teams should move toward Pervasive Security.
The creation of new digital products is usually organized around two parallel, interacting and complementary streams: one is dedicated to the implementation and evolution of the underlying technological platform; the other is focused on the lifecycle of business applications running on top of the enabling platform. These streams should be supported through dedicated security practices. Pervasive Security identifies three core practices: Progressive Security by Design for standardizing architectures via reusable patterns and making the enabling platforms foundationally secure, DevSecOps for integrating application security into Agile and DevOps paradigms, and Threat Modeling for identifying threats and related countermeasures by considering both the specific context and the whole ecosystem.
In addition, Pervasive Security foresees the introduction of the distributed security department, supported by a new, specialized security profile known as the Security Champion.
How can we help
Implementing and running Pervasive Security requires a new way of thinking and a set of technical, organizational, and methodological evolutions spanning across the whole organization.
Reply services can support its customers in every phase of the Pervasive Security lifecycle: from preparation, to implementation, to runtime. We begin with a consultation to assess the specific context and design the best evolution strategy from an organizational and technical point of view.
We work side by side with the customer to customize the methodology and related practices, select and integrate the needed tools, prepare the foundational assets, and facilitate the adoption process. Finally, at runtime, we offer our Security Champions to help execute Pervasive Security practices like DevSecOps and Progressive Security by Design and support their continuous improvement.